Security issue caused by the WebRTC feature
It is well known that the WebRTC feature in Chrome will leak your IP address even if you are behind a proxy server or using a VPN service. While most people who do not use proxy or VPN reveals their IP addresses to whatever web server they visit all the time, the IP address is the most easily accessible piece of information to track a website visitor. For the minimum, big companies such as Google and Facebook are using the IP addresses to analyzing your habits and behavior and send your highly-targeted ads. While most people are fine with targeted ads, there are people who don’t like to be tracked at all for whatever reason. They will choose to use either proxy or VPN service to avoid being tracked. However, in a browser which supports WebRTC, including Chrome, Slimjet and Firefox, the website owner can easily obtain the website visitor’s IP address by a simple piece of Javascript.
In addition to that, the WebRTC Media Device Enumeration API also enables the website owner to obtain a unique media device id from the user, which can be used to uniquely identify the visitor.
While Firefox provides an option to turn off the WebRTC feature, there is no such option available in Chrome, which isn’t completely surprising considering the fact that Chrome isn’t known fore being generous with options. There are people who mention this block WebRTC plugin. But in reality, this plugin can be easily bypassed and fails to work in all cases.
How to disable WebRTC in Slimjet
To address this security issue, we have provided a built-in option in Slimjet to easily disable WebRTC. If you have never used Slimjet before, Slimjet is based on the Chromium project while offers many more features and options to boost productivity and customizability. To disable WebRTC in Slimjet, select Settings from the menu, locate the option “Enable WebRTC” under the Security section as shown below,
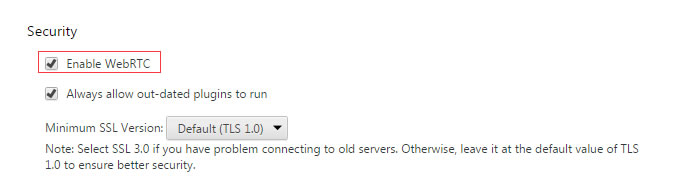
After uncheck the optoin “Enable WebRTC”, you will need close and reopen the tab for the setting to take effect.
How to verify the IP leackage issue is fixed
Here are three websites which can let you detect if your browser is liable to the IP leakage issue caused by WebRTC:
